How to Make a Resume for Today's Job Market
Learn how to write a resume that is optimized for applicant tracking systems (ATS) with our step-by-step guide.
Build New Resume-
Jobscan customers have interviewed with:
-
-
-
-
-
-
Writing a resume today is a whole new ball game compared to the past. Not only has the job market changed, but technology has revolutionized the way resumes are reviewed and selected.
This revolutionary technology is called an applicant tracking system, or ATS. It’s computer software that most companies use to sort and filter the large volume of resumes they receive.
Most job seekers aren’t aware of the ATS and how it can impact their resume’s chances of getting noticed by employers.
This means you can gain a competitive advantage simply by creating a resume that is optimized for ATS technology.
This article will take you, step-by-step, through the process of creating an ATS-optimized resume.
Before diving into the nitty-gritty of creating your resume, here’s a quick overview:
- Choose a format – Select a resume format that suits your needs. We recommend the chronological or hybrid format.
- Add your contact details – Include your name, phone number, and email address. You can also include your LinkedIn profile or personal website.
- Write your resume headline – This is a concise, one-line description of who you are as a candidate.
- Write a summary – This is a brief statement that highlights your main skills, experience, and career goals.
- Identify important keywords – Read the job description and note the skills and keywords that appear the most. Hiring managers are looking for these keywords, so make sure to include them on your resume.
- List your work experience – Include the company name, job title, and dates of employment. In a bulleted list, describe both your responsibilities and your achievements.
- Use action verbs – Start each bullet point with an action verb to make it more dynamic and engaging.
- Use numbers – Whenever possible, use numbers when describing your achievements to show the impact you had.
- Tailor each resume – Customize your resume for each job by including keywords from the job description to make it more relevant.
- Create a skills section – Highlight your skills and abilities relevant to the job you’re applying for.
- List your education – Include your degrees, schools attended, and relevant coursework.
- Include additional sections – Add sections for certifications, volunteer work, hobbies, or any other relevant information.
- Format your resume for the ATS – Make sure your resume can be read and properly parsed by an ATS.
- Proofread and edit – Carefully review your resume for spelling or grammatical errors. Consider asking someone else to proofread it as well.
- Keep it concise: Aim for a one- or two-page resume. Be selective with the information you include, focusing on the most relevant and impactful details.
- Save and send appropriately – Save your resume as a Word document or PDF. When sending electronically, use a professional email subject line.
Step #1 - Choose the right resume format
A resume format is the way you organize your information. The goal is to present your qualifications, work history, and skills in a clear and cohesive way.
There are three standard resume formats to choose from – chronological, functional, and hybrid.
1) Chronological resume format
This is the most popular resume format, especially for job seekers with lots of relevant experience.
The chronological resume format lists your work history in reverse chronological order, with your most recent jobs listed first.
The chronological format is ideal for:
- Job seekers with a lot of professional work experience.
- People with no employment gaps.
- Those who want to showcase their career progression over time.
2) Functional resume format
This resume format focuses on your skills rather than your work history. It helps you downplay your lack of experience in a particular field.
Recruiters don’t like the functional resume format. It can make it seem like you’re trying to conceal something. So be wary of that.
Under each skill you list, try to add bullet points that provide specific examples of times when you’ve used that skill.
The functional format is more suitable for:
- Recent graduates
- Entry-level job seekers
- Career changers
- Those with gaps in their employment history
3) Hybrid resume format
A hybrid resume is a combination of the chronological resume and the functional resume. It showcases both your work history and your skills.
With this format, you begin with an overview of your skills. This is followed by a reverse-chronological listing of your employment history.
We like the hybrid resume because it offers the best of both worlds, combining the strengths of the chronological and functional formats.
The hybrid format is ideal for:
- Mid-level job seekers with some experience in their field.
- Career changers who need to highlight transferable skills.
- People reentering the workforce.
Step #2 - Add your contact information
This is one of the most important sections of your resume. If hiring managers can’t contact you, it doesn’t matter how great the rest of your resume is.
The following information should appear at the top of your resume.
- Name
- Phone number
- Location (City, State, Zip Code)
- Email Address
- LinkedIn profile URL
Here’s an example:

It’s surprising how often job seekers forget a crucial piece of contact information.
Double-check to make sure it’s as easy as possible for recruiters to contact you for a job interview.
Contact information do’s and don’ts:
- Never include a work phone number, only a personal number.
- Don’t include more than one phone number or email address. This will only confuse hiring managers.
- Unless required, don’t include your date of birth. Employers may unknowingly discriminate against older job seekers. It can also make it easier for identity thieves to commit fraud.
- Don’t use a quirky or unprofessional email address. Instead create a new professional sounding address just for your job search. Research has shown that formal email addresses perform better on resumes than informal ones.
- Unless required, don’t put a picture on your resume. How you look isn’t important, and a photo takes up valuable space on your resume.
- If you use an outdated email service like Hotmail or AOL, consider creating a free Gmail account for your job search.
- Include your full name, including your middle initial if you have one. This will help ensure that you’re easily found in online searches.
- If you have an unusual name or a name that could be easily mispronounced, consider including a phonetic spelling to avoid confusion.
- You don’t need to include your full address but do add your city, state, and zip code. Recruiters often search for local candidates first.
- Include a link to your professional website or online portfolio, if you have one.
- Create a strong LinkedIn profile and be sure to include the URL on your resume (make sure it’s up to date).
Step #3 - Write your resume headline
One way to make sure your resume stands out is to write a catchy resume headline. This is a one-line description of who you are as a candidate.
A well-written headline that concisely presents your most relevant skills and experience can grab a recruiter’s attention and encourage them to read further.
Place your headline near the top of your resume, so it’s one of the first things that a hiring manager or recruiter sees.
Here’s an example:

Resume headlines are most beneficial for people who have a lot of relevant experience. But anyone can use them.
What if you don’t have any work experience or are applying for an entry-level job?
You can still use your resume headline to show off:
- Your soft skills.
- Your experience using tools.
- Your winning personal attributes.
To optimize your headline for the ATS, try to include the job title of the position you’re applying for. You can find the job title in the job description.
This way, when hiring managers search through the ATS for suitable candidates, your resume is more likely to be found.
Resume headline do’s and don’ts:
- Don’t make your headline too long or it will lose the reader’s attention. Keep your headline under ten words to make sure it packs a punch.
- Avoid using jargon. Stick to language that can be easily understood by everyone.
- Don’t be too salesy. A resume headline is not the place to make a hard sell; instead, focus on giving a snapshot of your skills and experience.
- Steer clear of clichés. With so many resumes to sift through, recruiters will appreciate a fresh, original headline that cuts to the chase.
- Always tailor your headline to each job you apply for.
- Use title case (capitalize the first letter of each word) and use a bold or slightly larger font so the headline stands out visually.
- Position yourself as an expert in your field. This can help to set you apart from other candidates who may not be as confident in their abilities.
- Use numbers and statistics to back up your claims. The applicant in the example above uses “5 years experience” to highlight their area of expertise.
- Use attention-grabbing action verbs. The example above uses the verb “leading,” which quickly tells employers what the applicant has accomplished.
- Be specific. Generic phrases such as “hard worker” or “team player” are nice, but they don’t really tell employers anything. If you can, include a specific accomplishment or skill that makes you stand out from the rest.
Step #4 - Write your resume summary or objective statement
Most recruiters only spend between six and eight seconds looking at a resume before they make a decision about a job candidate, according to a study by Ladders.
This means you need to make a strong first impression!
You can do this by adding a resume summary underneath your headline. This is a brief paragraph or a set of bullet points that summarizes your professional qualifications.
Your summary should expand on your headline. It does this by highlighting your skills, achievements, and experience.
Here’s an example:

A resume summary is particularly effective for experienced professionals or those with a solid track record in a specific field.
To optimize your summary for an ATS, try to include keywords and skills from the job description.
Resume summary do’s and don’ts:
- Don’t make bold claims that cannot be backed up.
- Don’t just list your job duties; instead focus on your accomplishments.
- Don’t include personal information unrelated to the job.
- Avoid using personal pronouns (I, me, or my).
- Keep it brief – no more than a few sentences or bullet points.
- Look for patterns in your work history – anything that you can point to and say “this is what I do, and I’m good at it.”
- Focus only on your most relevant skills and experience.
- Use numbers and specifics to show that you are a results-oriented individual who is able to produce tangible outcomes.
- Incorporate keywords from the job description whenever possible.
- Tailor your summary statement to each job you apply for.
If you are applying for an entry-level job or are changing careers, you could write a resume objective instead of a summary.
Your resume objective basically explains what the object of your resume is. It is a short statement that communicates your reason for wanting to work in a new field.
It should include:
- The job title or field you are interested in.
- Any transferable skills that make you a good fit for the position.
- Relevant accomplishments that demonstrate how you would excel in the new role.
- Your career goals and how the position you are applying for can help you achieve them.
For example, if you are a recent college graduate seeking a position in marketing, your resume objective might state:
“To secure a position in marketing where I can utilize my creativity and analytical skills to contribute to the company’s success.”
Step #5 - Identify important keywords and skills
We’ve already talked about using resume keywords when you write your headline and your summary, but now it’s time to delve deeper.
After you submit your resume it goes into an ATS database. Hiring managers use the database to search for the most qualified job candidates.
How do they search? By typing keywords into the search bar of the ATS. These keywords are the same ones that appear in the job description.
If your resume contains these keywords, it will probably show up in the search. But if your resume does NOT contain these keywords, it will probably sit in the database, never to be found.
This is why you must identify the most important keywords for every job you apply to. Your resume should not be a one-size-fits-all document!
Tailoring each resume to a specific job takes more time and effort (which is why most job seekers don’t do it). But it will give you a definite advantage over your competitors.
One way to do this faster is to use a tool like Jobscan’s resume scanner. It compares your resume to the job description and produces a Match Report. This report highlights the skills and keywords you should try to add to your resume.
Here’s an example of a Match Report:

In the above example, the term “required” means that those skills are crucial qualifications for the job.
If you can, add the keywords “ms office” and “google suite” to your resume. This will make it easier for hiring managers to find it when they search through the ATS for job candidates.
You can try the Jobscan resume scanner for free below.
Step #6 - Create your resume work experience section
Now it’s time to get to the heart of your resume – the work experience section. This is the section employers will spend the most time looking at when they consider your resume.
The first things a recruiter looks at on your resume are:
- The job titles you’ve held.
- The companies you’ve worked with.
Make this information easy to find by listing each job in reverse-chronological order (latest job first).
Each job should have its own subheading that includes the following information:
- Company name and location – Include the full name of the company you worked for followed by the city and state of its location.
- Job title – Be as specific as possible to ensure that employers know exactly what your role was within the company.
- Start and end dates – Include the month and year for each position. If you only list the year, it may appear as though you are omitting information.
- Achievements and responsibilities – These can be listed using bullet points. Include hard numbers and metrics wherever possible. To create bullet points quickly, try Jobscan’s free bullet point generator.
Our research has found that the above sequence offers maximum applicant tracking system (ATS) compatibility.
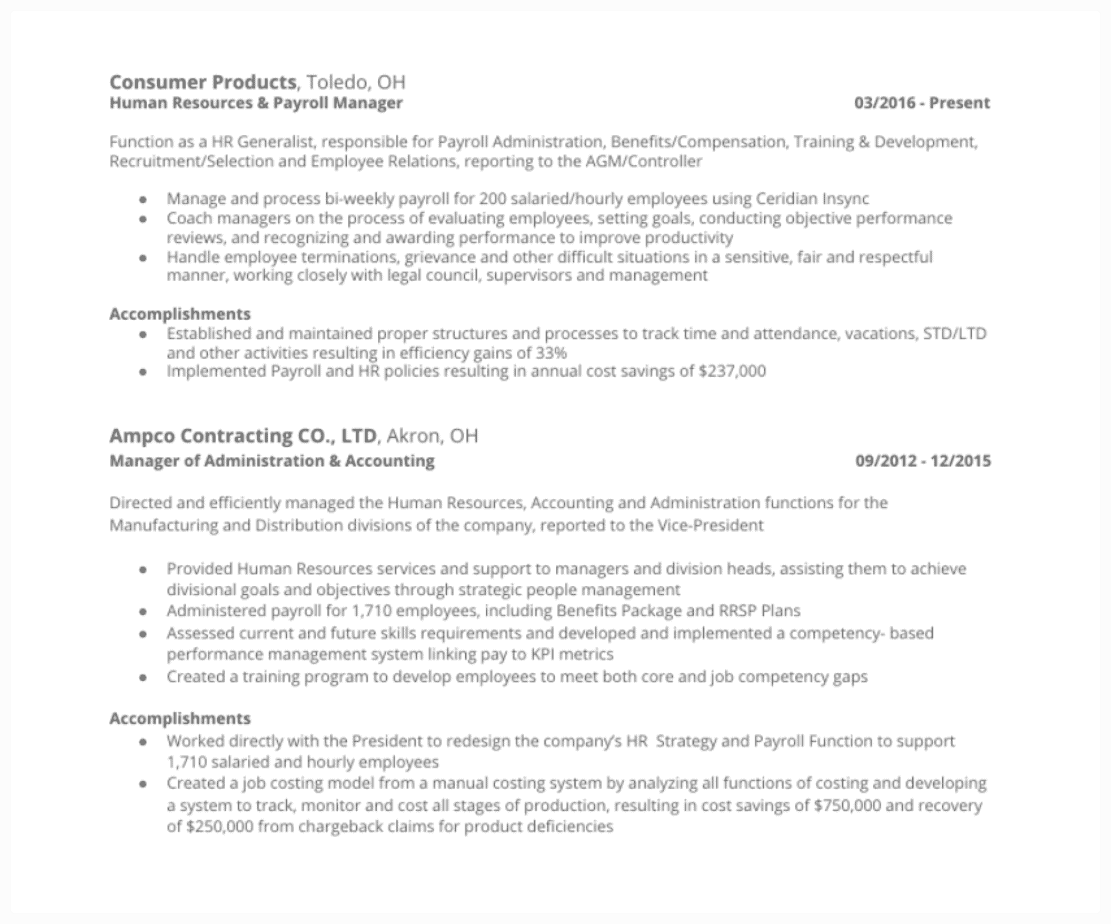
Here’s an example:
Work Experience Tip #1 – Highlight achievements as well as responsibilities
One of the biggest mistakes people make when writing a resume is only listing their job responsibilities. These are tasks that you’re expected to perform as part of your job.
They can include things like:
- Answering customer questions and complaints.
- Scheduling and coordinating appointments.
- Taking inventory and ordering supplies.
- Maintaining records and filing paperwork.
- Training new employees.
Listing your job responsibilities gives a potential employer an idea of what you did day-to-day. But it doesn’t reveal how well you did it.
That’s why it’s important to highlight your specific accomplishments in prior roles.
For example, if you increased sales, reduced costs, or implemented new processes or technologies, be sure to mention these accomplishments.
Instead of saying,
“Managed a team of 12 people.”
You could say,
“Managed a team of 12 people, consistently meeting or exceeding quarterly targets.”
This demonstrates that you are an asset to any organization. It also gives employers confidence that you’re capable of handling the job.
Here’s an example of a resume that does a good job of listing both responsibilities and accomplishments:

Not every career lends itself to easily-quantifiable achievements. For example, someone who works in a warehouse might have responsibilities that include:
- Stocking shelves.
- Unloading trucks.
- Packaging items for shipment.
These responsibilities might not seem like much. But they’re essential for keeping the warehouse running smoothly. The ability to work efficiently and effectively is a valuable skill in any field.
So, next time you’re feeling like you don’t have anything to list as an accomplishment, take a step back and look at the bigger picture. Chances are, you’ve achieved more than you realize!
Work Experience Tip #2 – Use action verbs
Action verbs increase the overall impact of your resume. They bring energy and clarity to your work experience.
Action verbs describe how you did something. Examples include “achieved,” “implemented,” “led,” “created,” “organized,” “resolved,” and “innovated.”
Don’t just say you were “responsible for” a task. Instead, explain how you took charge and made it happen.
For example, you could say that you “spearheaded a new project” or “coordinated team members.”
Action verbs make your resume more compelling to read. They also demonstrate a proactive attitude that appeals to employers.
Work Experience Tip #3 – Use active voice, not passive
Always try to use an active voice instead of a passive voice when writing your resume.
In an active voice, the subject of the sentence is doing the verb. In a passive voice, the subject is being acted upon by the verb.
Active voice,
“The chef prepared the meal.”
Passive voice,
“The meal was prepared by the chef.”
Active voice is preferred over passive voice because it’s more direct, concise, and easier to read. It also makes you sound more confident and authoritative.
For example, “managed a team of 12” is more powerful than “was responsible for a team of 12.”
Work Experience Tip #4 – Use numbers
One of the best ways to make your resume stand out is to use numbers.
In fact, job seekers who use numbers in their resumes increase their hireability by 40%, according to a study by TalentWorks.
Whenever possible, quantify your achievements with numbers that illustrate the scope of your work.
Instead of saying,
“Created marketing campaigns.”
You could say,
“Created 10 successful marketing campaigns that generated a 20% increase in leads.”
By using numbers, you give hiring managers a better sense of your value. This makes it more likely that you’ll land the job you want.
Here are some more examples of using numbers (with action verbs underlined):
- Saved $7 million while introducing nationwide transport service for medical patients.
- Successfully increased sales by 20% within the first quarter of implementing a new marketing strategy.
- Streamlined project management process, reducing overall project completion time by 15% and improving team efficiency.
Work experience do’s and don’ts:
- Don’t list more than 10-15 years of work experience unless it’s highly relevant.
- Don’t list every single task you worked on; include only the most relevant.
- Don’t use the same, tired words (“responsible for…”); instead use action verbs written in an active voice.
- Don’t lie or exaggerate about your duties and accomplishments.
- Use a traditional section heading like “Work Experience” instead of a more creative option like “Where I’ve Been,” which will confuse the ATS.
- When writing dates, use the mm/yyyy format, which can be easily parsed by an ATS.
- Use past tense when talking about jobs in the past, and present tense when describing the work you are currently doing.
- Leave out personal pronouns (I) and get right to the action.
- Tailor each and every resume to the specific job you’re applying for.
- Consider tracking your job achievements on a spreadsheet so you can easily include them on your resume later.
Step #7 - Write your resume skills section
A resume skills section allows hiring managers to quickly assess your key abilities and qualifications.
Begin by identifying the most important skills listed in the job description. Then add them to your resume if you can.
There are two types of skills: hard skills and soft skills.
Hard skills are the specific skills and knowledge that you need to perform a certain task or job. They are usually quantifiable and easy to measure.
Examples of hard skills include:
- Computer programming
- Copywriting
- Data analysis
- Programming
- Accounting
- Graphic design
- Web development
- SEO
Soft skills, on the other hand, are abilities that help you work well with others. These interpersonal skills are more difficult to quantify than hard skills but are just as important in the workplace.
Examples of soft skills include:
Soft skills are important because they’re transferable. This means they can be applied to any number of settings and can help you succeed in any type of job.
Also, unlike hard skills, which can become outdated quickly, soft skills are always in demand.
As the world changes and technology advances, soft skills will become even more important.
Here’s an example of a skills section for a mechanical engineer that includes both hard and soft skills:

The best way to find relevant skills to add to your resume is to use an online tool like Jobscan’s resume scanner.
The scanner will analyze your resume against the job description and tell you exactly which hard and soft skills to include. Adding these skills makes it more likely that a hiring manager will find your resume when searching through the ATS.
Step #8 - Add your education and training
You need to include an education section somewhere on your resume. Where it appears depends on your individual circumstances.
Are you just starting out in your career?
If so, feature your education section near the top of your resume. Recent grads can include relevant coursework, societies, organizations, and extracurriculars that strengthen their candidacy.
Are you a few years into your career?
If so, then your education can appear lower down on your resume. This is because your work experience is more relevant at this point in your career.
If you’re applying to a job that requires extensive education (like medicine, law, or academia), you’ll need to be more detailed. But most job seekers can get away with providing only the following information on their resume:
- Name of school
- School location
- Degree
- Year graduated
If you’ve earned any professional certifications that are relevant you should list them right under your education information.
Be sure to include:
- The name of the certification.
- The issuing authority.
- The date of certification.
- If the certification is still valid, mention that.
- If you have earned multiple certifications, list them in order of importance. The most relevant ones should appear first.
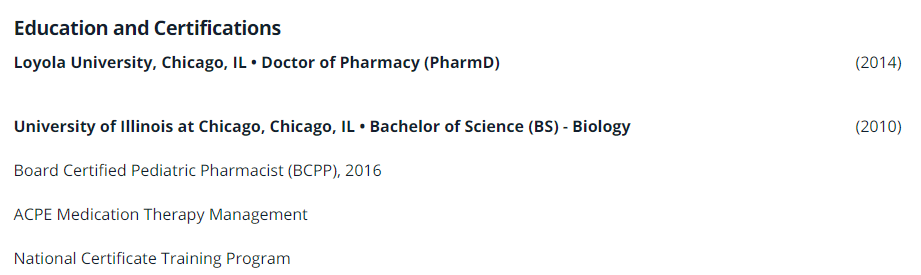
Here’s an example of what the education section looks like on a pharmacist’s resume:
Education section do’s and don’ts
- Don’t mention your high school if you have a university degree.
- Don’t disclose your GPA unless you graduated recently and had a very impressive academic career (3.5 GPA plus).
- Don’t lie about your education!
- List your educational achievements in reverse chronological order, with your most recent qualifications first.
- Include any relevant coursework, skills training, licenses, and certifications.
- If you’re still pursuing your education, you can list your expected graduation date.
- Include extracurricular activities, but only if they’re relevant.
- If you studied abroad, include information about the program and what you did there.
Step #9 - Additional resume sections (optional)
Your resume is your opportunity to shine. It’s your chance to show potential employers who you are and what you’re capable of.
One way to really stand out is to include additional information that showcases your skills and accomplishments.
If applicable, consider adding the following resume sections:
Languages
In today’s global economy, knowing foreign languages can give you a competitive edge over other candidates. Many businesses are looking for employees who can speak with customers and clients in their native language.
On your resume, list the languages you speak. Start with your strongest language. Also, specify whether you are fluent, proficient, or conversational in each language.
For example:
- Fluent in Spanish and English.
- Fluent in French and conversational in German.
- Conversational in Japanese.
Hobbies and interests
Many people believe that hobbies should remain separate from their professional lives. Not necessarily!
Your hobbies can give employers a better sense of who you are as a person.
For example, if you enjoy hiking, it shows that you are physically active and have a sense of adventure. If you enjoy cooking, it shows that you are creative and have a keen interest in food.
When listing your hobbies, make sure to keep it short and sweet. You don’t need to go into great detail about every single hobby you have.
Just mention a few that you think are relevant and leave it at that.
Publications
Have you ever been published in any capacity? Include this information on your resume, especially if it’s relevant to the job you’re applying to.
Most employers love to see that you can communicate effectively in writing!
If you’re not sure where to start, list any published articles, blog posts, books, or even whitepapers that you have written.
Be sure to include the title, publisher, and date. For example:
“The Impact of Social Media on Businesses.” The Journal of Business, December 2021.
Have you won any awards that are relevant to the job you’re applying to? If so, you should absolutely include them on your resume.
Awards will impress potential employers and help you to stand out from the competition.
Be sure to list:
- The name of the award.
- The date you received it.
- A brief description of the award.
For example:
“Top Salesperson” (January 2020) – Awarded to the salesperson with the highest sales numbers for the month.
Volunteer experience
If you have any volunteer experience, don’t forget to add it to your resume.
According to a LinkedIn survey, 20% of employers say they have hired a candidate because of their volunteer experience. The survey also showed that job seekers who volunteer are 27% more likely to be hired than non-volunteers!
When adding your volunteer experience to your resume, list:
- The name of the organization.
- The dates of your service.
- A brief description of your duties and responsibilities.
For example:
Woodstock Food Bank, Jan 2019-present
- Led a team of 10 volunteers in sorting and distributing donated items to local families in need.
- Organized monthly food drives that collected an average of 500 lbs of food per month.
Personal projects
Many professionals use their skills outside of the office. In fact, 57 million workers participate in the gig economy in the United States.
Adding your side projects to your resume can be a great way to show your commitment to lifelong learning and professional development.
Examples of personal projects include:
- Designing websites.
- Creating a YouTube channel.
- Coding apps.
- Writing a book.
- Running an e-commerce store.
- Consulting.
- Starting any kind of new business.
When choosing personal projects to include on your resume, be sure to select those that are most relevant to the position you are applying for.
Step #10 - Format your resume so it can be easily read by an ATS
When an ATS receives your application, the first thing it does is parse your resume.
Parsing involves extracting the information from your resume and organizing it so it can be easily scanned.
Unfortunately, many resumes contain formatting errors that prevent the ATS from parsing them correctly.
These resumes might be perfectly tailored for the job and have all the right keywords, but they’ll never be seen…all because of simple formatting errors.
To prevent this from happening to you, pay close attention to these formatting do’s and don’ts!
Formatting do’s and don’ts
- Don’t use tables and columns to organize your resume. This can cause important information to get lost when an ATS scans your resume.
- Don’t use unnecessary graphics or embellishments that might be difficult for an ATS to understand.
- Don’t use special characters or symbols that an ATS might misinterpret.
- Don’t make your resume longer than one page, unless absolutely necessary.
- Use language that is simple and easy to understand. Jargon or difficult language will only confuse the ATS.
- Use a common font such as Times New Roman, Arial, or Helvetica for optimal readability.
- Use a font size that is easy to read. The recommended size is 11-12 pt for regular text, and 14-16 pt for section titles.
- Make sure that the margins on all sides of your resume are 1 inch so that it doesn’t look too crowded.
- Use a Word document when you are creating your resume. This will ensure that it looks good and is easy for the ATS to read.
- Make sure to proofread your resume for mistakes before you send it off.
Check every resume you send out to make sure it’s formatted correctly. One mistake can reduce your chances of getting a job interview.
Use Jobscan’s resume scanner to quickly identify any formatting issues you need to address.

Step #11 - Add a cover letter
When you submit your resume, you’ll most likely also have to submit a cover letter. Think of a cover letter as a quick preview of your skills and experience.
The best cover letters are usually short so the message is clear and easy to understand.
How to Write a Cover Letter:
- Contact Information – Include your full name, address (including zip code), and phone number with area code. Your contact information should be in the upper left corner of your cover letter.
- Greeting – Ideally, you should find out the name of the hiring manager and greet them directly. To find the hiring manager’s name, search the company website. You can even call and ask which hiring manager is assigned to this particular position.
- Opening – Think of your opening sentence as your chance to grab the hiring manager’s attention and get them excited to learn more about you. What can you do that nobody else can?
- Body – You need to sell yourself in this section. The best way to do this is by providing examples of your measurable accomplishments. These are powerful because they show tangible proof of your abilities. Only include the most relevant and positive information about yourself in your cover letter.
- Closing – This section is used to thank the hiring manager for their time and to point out any attachments (website, portfolio, samples). Be professional and don’t sound too eager, or you might sound desperate.
- Use Keywords – If you can, use some of the same keywords from the job description in your cover letter. This will show employers that you have read through the job description carefully and that you understand what they are looking for in a candidate.
A great cover letter allows employers to see beyond your resume. It gives employers an idea of who you are as a person—and if you would be a good fit for their company culture.
When you’re done writing your cover letter, run it through Jobscan’s cover letter checker. It will tell you how to improve your cover letter.
If you don’t want to spend too much time writing a cover letter, use Jobscan’s cover letter generator. This tool uses GPT-4 technology to generate an ATS-friendly cover letter in just one click.
Step #12 - Proofread your resume
Proofreading is one of the most important things you can do before sending off your application. A single typo or mistake can make you look unprofessional and could cost you the job.
To help you proofread, there are free grammar and spell-check tools that you can find online. Here are two we recommend:
Grammarly – This is an online writing assistant that provides real-time grammar, spelling, punctuation, and style suggestions.
Hemingway Editor – This writing tool improves readability by highlighting complex sentences, excessive adverbs, and other areas that can be simplified for clearer communication.
It’s also a good idea to have someone else read your resume. Fresh eyes can find mistakes that you missed.
The best way to find mistakes is to run your resume through an online tool like Jobscan’s resume scanner. It will quickly identify any formatting issues or other errors that can prevent an ATS from reading it properly.
8 resume examples for different jobs
Now that you know how to write a resume for today’s job market, it’s time to look at some examples.
Each one of these resume examples is followed by an explanation of why they work. Use these examples for both guidance and inspiration when you’re working on your own resume.
1. Sales manager resume example

Why this resume works:
- Easy to skim and visually appealing. The touch of blue color enhances its aesthetic appeal.
- Begins with the most recent work experience, ensuring a clear and logical progression.
- Effectively captures the job seeker’s extensive 25+ years of experience through a detailed summary.
- The skills section includes all the core competencies and important keywords relevant to the desired position.
- The work experience section highlights notable accomplishments supported by concrete statistics and figures.
- There are no headers, footers, images, or tables to prevent an ATS from reading it accurately.
2. Accountant resume example

Why this resume works:
- Highlights the job seeker’s strong professional background and experience.
- Showcases measurable achievements and results.
- Adds the job title CPA next to their name.
- Features technical skills and knowledge of different accounting software.
- Uses relevant keywords.
- Use of color enhances rather than overwhelms.
3. Recruiter resume example

Why this resume works:
- Highlights relevant accomplishments in the work experience section.
- Simple formatting makes it easy for both ATS and humans to read.
- The resume summary highlights the job seeker’s role as the founder and strategic leader of her organization.
4. Bookkeeper resume example

Why this resume works:
- The resume summary highlights skills and knowledge of accounting software.
- Includes relevant keywords in the summary and work experience sections.
- Bullet points feature measurable achievements.
- Mentions certification in bookkeeping and a degree in accounting.
- Incorporates relevant technical skills in accounting and industry keywords like US-GAAP.
5. Digital marketing resume example

Why this resume works:
- Showcases essential marketing skills immediately following the resume summary.
- The work experience section highlights notable achievements related to the job.
- The resume summary emphasizes the job seeker’s years of experience, dedication, extensive industry knowledge, and proficiency with digital tools and technologies.
6. Teacher resume example

Why this resume works:
- Highlights important skills that preschool teachers need, including both core competencies and hard and soft skills.
- Begins each bullet in the work experience section with a powerful action verb.
- Showcases measurable achievements and tangible results.
7. Customer service resume example

Why this resume works:
- Begins with a powerful resume summary highlighting the job seeker’s four years of work experience and exceptional communication and interpersonal abilities.
- Includes relevant keywords throughout the resume.
- Lists relevant skills in the skills section, even those outside of the industry, such as marketing, sales, and event planning.
8. Office assistant resume example

Why this resume works:
- Begins with a compelling resume summary that highlights the job seeker’s strong experience in administrative work and her various skills and abilities.
- The summary includes keywords that are relevant to the desired position.
- Provides a detailed overview of measurable achievements and important job responsibilities, while incorporating relevant keywords throughout.
Step #10 - Format your resume so it can be easily read by an ATS
FAQs
The benefit of using a resume template is that you don’t have to start from scratch. Templates provide a pre-designed structure that you can simply fill in with your own information.
Remember to tailor each resume to the job you’re applying to, and always proofread thoroughly.
Resume builders are helpful for those seeking a convenient and efficient way to create a resume without extensive design or formatting skills. Here is our list of the top 10 free resume builders.
If you have no work experience to put on your resume, focus on highlighting your transferable skills, education, and any relevant coursework, internships, volunteer work, or extracurricular activities.
Start with a concise objective or summary statement that highlights your enthusiasm and willingness to learn.
Many people believe that a CV and a resume are the same thing. This is not the case.
CV stands for curriculum vitae. It is typically longer and more detailed than a resume. A CV focuses on a person’s academic background. CVs are commonly used in academic, scientific, or research-oriented fields.
On the other hand, a resume is shorter and focused on skills and work experience. Resumes are commonly used in business, corporate, or non-academic settings.
Today’s resume should have a clean and professional design, and be optimized for applicant tracking systems (ATS).
Make sure you tailor each resume for the specific job you’re applying to. The best way to do this is to include the same keywords that appear in the job description. Don’t use graphics, images, or elaborate formatting that may confuse the ATS.
By following these basic guidelines, you’ll increase the chances that your resume will pass the initial ATS screening and reach the hands of a human recruiter.
To learn more, here are 60 resume tips to help you land interviews.
Employers generally prefer a clean, concise, well-structured resume. It should highlight your skills and experiences relevant to the job you’re applying for.
Recruiters generally prefer the chronological or hybrid resume formats over the functional format. These two formats present your work history in reverse chronological order, starting with your most recent position.
The functional resume format can raise red flags for recruiters. This is because it does not provide a clear, detailed picture of your work experience and job progression.
Generally speaking, you should only include the last ten to fifteen years of work history on your resume. There’s no need to list jobs from more than fifteen years ago unless they’re highly relevant and demonstrate a significant achievement or skill.
To write a resume on Google Docs, start by opening Google Docs and signing in to your Google account. Browse through the Template Gallery to select a resume template that suits your needs.
Customize the template by filling in your own information. Format the document to your preferences, and add or remove sections as necessary.
Finally, save the document in your Google Drive or download it in a preferred format like PDF or Word. Here are some free Google Docs templates you can use to help you create your resume.
Yes, you can use ChatGPT to help write your resume. It can assist in structuring the resume, suggesting appropriate wording, and tailoring content to highlight your skills and experiences effectively.
Explore more resume resources









